Software encryption has some drawbacks. Because the processor is working to encrypt and decrypt the data, it can slow down system performance. Because the encryption method uses the drive, rather than the CPU, there is no slow down in performance. The Crucial® MX-series SSDs have a 256-bit AES encryption controller.
Hardware-based encryption uses a device's on-board security to perform encryption and decryption. A hardware-based solution is most advisable when protecting sensitive data on a portable device such as a laptop or a USB flash drive; it is also effective when protecting data at rest.
With hardware encryption on secure USB drives, the AES encryption process is handled automatically, built right in with a small chip inside the drive itself. Once original data is encrypted, it becomes undecipherable in the background and is locked away under encrypted storage within the drive.
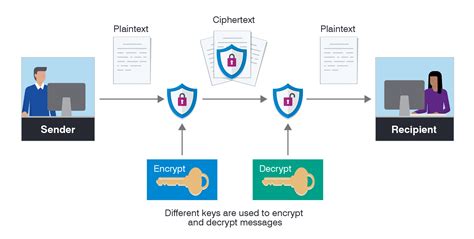
Encryption is the process of taking plain text, like a text message or email, and scrambling it into an unreadable format — called “cipher text.” This helps protect the confidentiality of digital data either stored on computer systems or transmitted through a network like the internet.
Encryption software is software that can encrypt data and files to help keep sensitive data secure. In this lesson, learn about its history as well as different keys needed to decrypt the software.
The Advanced Encryption Standard (AES) is a symmetric block cipher. A cipher is a method for converting data from an unencrypted into an encrypted format. The encrypted data is also referred to as cipher text.
What is not a role of encryption? Explanation: Encryption doesn't have error correction or detection facility thus cannot be used to safeguard from data corruption.
There are two types of encryption in widespread use today: symmetric and asymmetric encryption. The name derives from whether or not the same key is used for encryption and decryption.
Advanced Encryption Standard
The company that manufactured them, Pektron, only used a 40-bit encryption protocol, which was relatively easy to break. To fix the problem, Tesla and Pektron transitioned the fobs to 80-bit encryption, which should have been wildly more challenging to break.
See encryption algorithm and cryptography. Encryption is defined as the conversion of something to code or symbols so that its contents cannot be understood if intercepted. When a confidential email needs to be sent and you use a program that obscures its content, this is an example of encryption.
Encryption converts data into ciphertext, preventing hackers from accessing it in most cases. Encryption only protects whatever is encrypted, such as your internet connection, email or files, but it does nothing to protect you from other online threats.
AES 256 is virtually impenetrable using brute-force methods. While a 56-bit DES key can be cracked in less than a day, AES would take billions of years to break using current computing technology. Hackers would be foolish to even attempt this type of attack. Nevertheless, no encryption system is entirely secure.
On computers using the Windows 2000 operating system you will need to right click the file or folder, select Properties and click the Advanced… button. If the Encrypt contents to secure data checkbox is selected the files are encrypted.
The NAND Flash SSD and EncryptionThe nature of flash makes it more difficult to encrypt or erase data on SSDs than traditional hard drives. However, hardware-based disk encryption makes it easier than ever to encrypt and erase SSDs securely, and without any load on the Flash Controller.
Does whole-disk encryption only affect performance while the computer is starting or does it have constant effect on the computer's overall performance? Neither and both, actually. Encryption in general, and whole-disk encryption specifically, has come a long way since it was first introduced many years ago.
Why Does BitLocker Trust SSDs? When available, hardware-based encryption can be faster than software-based encryption. So, if an SSD had solid hardware-based encryption technology, relying on that SSD would result in improved performance.
BitLocker uses AES encryption with a 128-bit key. The X25-M G2 is announced at 250 MB/s read bandwidth (that's what the specs say), so, in "ideal" conditions, BitLocker necessarily involves a bit of a slowdown. However read bandwidth is not that important.
The abbreviation “SED” stands for “self-encrypting drive.” An SED is a hard disk drive (HDD) or solid state drive (SSD) with an encryption circuit built into the drive. It transparently encrypts all data written to the media and, when unlocked, transparently decrypts all data read from the media.
When enabled, the entire contents of the startup drive are encrypted. FileVault is easy to enable in System Preferences > Security & Privacy, and then once the intial encryption is over, it won't even slow your Mac down day to day.
Step 1: Enable encrypted drive
- Download and install the Samsung Magician software on the computer with the SSD drive.
- Open Samsung Magician and select 'Data Security' from the left hand menu.
- Make sure the correct drive is selected under 'Target Drive'
- Under 'Encrypted Drive' click 'How to enable'
- Download and install an encryption program, such as TrueCrypt, AxCrypt or StorageCrypt.
- Plug in your external hard drive to your computer and wait for your computer to detect it.
- Open your encryption program and select the option to create a new volume.
- Choose the password you want for access to this drive.
Because there is no known method of calculating the prime factors of such large numbers, only the creator of the public key can also generate the private key required for decryption. RSA is more computationally intensive than AES, and much slower. It's normally used to encrypt only small amounts of data.
Here are six tips for ensuring that encryption keeps you secure:
- Do Not Use Old Encryption Ciphers.
- Use Longest Encryption Keys You Can Support.
- Encrypt in Layers.
- Store Encryption Keys Securely.
- Ensure Encryption Implementation Is Done Right.
- Do Not Ignore External Factors.
The only unbreakable cryptosystem known - the Vernam cipher. Of all the methods of encryption ever devised, only one has been mathematically proved to be completely secure. It is called the Vernam cipher or one-time pad. The worth of all other ciphers is based on computational security.
A block cipher takes a block of plaintext bits and generates a block of ciphertext bits, generally of same size. The size of block is fixed in the given scheme. The choice of block size does not directly affect to the strength of encryption scheme. The strength of cipher depends up on the key length.
Twofish is considered among the fastest encryption standards and is hence favoured for usage among hardware and software enterprises. It is freely available and hence makes it popular. The keys used in this algorithm may be up to 256 bits in length and only one key is needed.
There are three general classes of NIST-approved cryptographic algorithms, which are defined by the number or types of cryptographic keys that are used with each.
- Hash functions.
- Symmetric-key algorithms.
- Asymmetric-key algorithms.
- Hash Functions.
- Symmetric-Key Algorithms for Encryption and Decryption.
In cryptography, a cipher (or cypher) is an algorithm for performing encryption or decryption—a series of well-defined steps that can be followed as a procedure. An alternative, less common term is encipherment. To encipher or encode is to convert information into cipher or code.
AES uses a symmetric-key algorithm. This means that the same key is used for both encrypting and decrypting the data. Asymmetric-key algorithms use different keys for the encryption and decryption processes. Today, 128-bit encryption is standard, but most banks, militaries, and governments use 256-bit encryption.